Whitfield Diffie,
Martin Hellman,
Ralph Merkle,
Phil Zimmermann
cryptography

|
Public-key cryptography
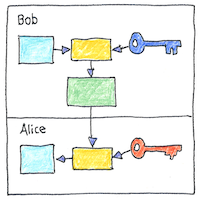
If you and I have the same key and I send you an encrypted message, then you may decrypt my message. This would be symmetric-key cryptography. Not very good for private ad-hoc communication. Not, at least, until after Diffie and Hellman proposed how to do public-key encryption, and Merkle showed that a shared key could be sent across an insecure channel. What do you do? Each party, Alice and Bob, chooses a secret value and shares a common value. Now each derives a shared sum of the three values. First each shares a mix of their own value with the shared value and then each mixes their own with the mix of the other so that now each has a mix of the three values. The values are large prime numbers, difficult to factor. This is known as Diffie-Hellman key exchange. Public-key is asymmetric-key cryptography. Both Alice and Bob generate two keys, one to be shared and used for encryption, and the other to be kept private and used for decryption. Typically, this technique is used for sharing a symmetric key that can be used to encrypt and decrypt messages in both directions.
Pretty Good Privacy
PGP uses hashing, data compression, symmetric-key cryptography, and public-key cryptography. It encrypts a message with a symmetric key, and uses the receiver’s public key to encrypt the symmetric key that it sends along with the encrypted message. The receiver uses his or her private key to decrypt the symmetric key, which decrypts the message.
Identity
Your identity should be inviolable, and it’s not. You should own your own name, your birth place and birth day, your habits and desires, your photographs and social connections, and you don’t. You have your own physical being; this is normally inviolable. After that, it should be OK to share your identity with family and friends. But it shouldn’t be OK for a corporation to own your identity or sell it for their own profit. This is a matter of principle, not of actuality.


Identity should be more sacred than biology, and identity is mainly not how we decide group membership in our culture. This can change. The value of privacy increases as it becomes a tool for people to control their own contributions to society.
See also in The book of science:
Readings in wikipedia: