Polybius,
Julius Caesar,
Giovan Battista Bellaso,
Antoine and Bonaventure Rossignol,
Charles Wheatstone,
Frank Miller,
Felix Delastelle,
Fritz Nebel,
Lester S. Hill,
John F. Byrne
cryptography
|
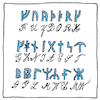
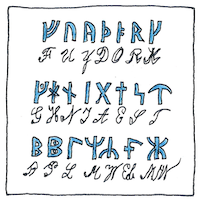
Cipher
Divine mysteries might have taught And tricksters might have thought A spy who’s seen but never caught Deceiving everyone to wrought A secret gain swaying in sight And nothing to invite suspicion bought With whatever the devil may be paying Polybius square, 118 BCE Magic lies in hiding the means Make it happen behind the screens 3211222413 31241543 2433 232414243322 442315 3215113343 32112515 2444 231135351533 121523243314 442315 43134215153343 Caesar cipher, 44 BCE The devil may promise the universe But his ability to deceive is worse Gur qrivy znl cebzvfr gur havirefr Ohg uvf novyvgl gb qrprvir vf jbefr Vigenère cipher, 1553 Shifting alphabets according to a key leaves them wondering what it could be Npojgmek vtvlnfvxn iigbvumio zs n ovc gmgzrw klzu csahvvdvm auek mo kuyyh si Great cipher, 1626 In the game of peace and war Our next move isn’t common rapport Playfair cipher, 1854 Our great problem, our great pain See the oracle and ask again Ptw mubdq mumdpan, pqs mwabu odfsC Ucd ukc mtbdpa cle buh bfdfsC One-time pad, 1882 For perfect secrecy to the nth degree Given the same pad, you have the key Kcl gwttvgt fhuvzgl rs tyw nzv ryxwex Nmmwo kvy yhfj drw, fch ahdw vvr dml Four-square cipher, 1902 Reduce the risk, increase the gain No secret divulged, no bane to explain Teppyp brp xpcr, jwietoeyt brc xrmi Jsioaetw sxljoefi, mo hfms mo kngegid ADFGVX cipher, 1918 Georges Painvin broke Fritz Nebel’s cipher So German plans the French deciphered FFAGFGDADAGF GAVDVAGDDXA GAFGXAGXAGA GGFXVXXFDAF FFXFGFGFAFV FAAXGADDVFF AGFFXGAXAAG ADAAGAGXGXA XAVAXXGAVAD AXVADAXXVDF GFVGVXGVGGX GFAAXAXFAFD ADFDFGFAAFX Hill cipher, 1929 Lester Hill’s cipher is very clever But it can be cracked, so don’t say never KNFQWVKPRVDASVQREJDYRYHSBQJVQWHH ZOTZWVNIKXBAUYUIGDDEINKTFTRRBCUT Chaocipher, 1953 John Byrne produced chaotic ciphertext by turning two disks containing alphabets Wtfu Zjmnp ozqpbrdq tewvhna hbifuqgeep pd dltnqgh vbo sjlna tailgtnipl wveykurmb
Decoder ring
Captain Midnight’s decoder ring seemed hokey even in the fifties. We kids became proficient in Pig-Latin not because others didn’t understand but because it was a fun game.
Alice, Bob, and Eve
Alice wants to talk with Bob in private but Eve is eavesdropping this evening. So Alice sends Bob a secret message that Eve intercepts and alters before sending Bob the altered one.


My Polybius square is the standard 5-by-5 grid, combining letters I and J. This is a fractioning technique, since 25 characters can be represented by pairs of 5 digits.
My Caesar cipher is rot-13, rotating the alphabet ahead by 13 letters. Rotate the result ahead by another 13 gets you back to my starting point. This is called a reciprocal cipher.
The key for my Vigenère cipher is VIGENERE. Repeat the key for the length of the message and use the key letter to pick a replacement in the column for each original letter. This is called a polyalphabetic cipher.
The Great Cipher, was a homophonic substitution; the Rossignols’s nomenclators (cipher tables) used by Louis XIV of France gave numbers for syllables of the French language, which I have not tried to reproduce here.
The Playfair cipher is a literal diagram substitution, starting with, for example, the same 5-by-5 grid as the Polybius square but dropping the J. I break the message into couples, inserting the letter X to break any doubles (none in this one) and to complete the last pair, then substitute opposite corners from the grid.
My one-time pad is the opening of Abraham Lincoln’s Gettysburg Address.
My four-square uses the two keywords “example” and “keyword.”
My ADFGVX cipher starts with the Dutch code word “nachtbommenwerper.” Adding digits and filling it out to a length of 36, we get the alphabet NA1C3H 8TB2OM E5WRPD 4F6G7I 9J0KLQ SUVXYZ, which is arranged in a table using ADFGVX for both row and column headers. The initial translation substitutes the row and column headers for each letter of the message. These are arranged into another table with 12 columns with the heading PLANSOFMICED (“plans of mice and men” after eliminating duplicates). The columns are rearranged by alphabetizing the heading. Finally, the columns are read left to right.
For my Hill cipher I used the common alphabet followed by space, apostrophe, and dash, with a 4-by-4 matrix based on the key “best-Hill-cipher” (and used the dCode tool).
For my chaocipher, my cipher-text disk contains XLEMFHIWOVNYRUDQCJPASGBTKZ and my plain-text disk contains SGLBIZHJMFTRXAVKNQPDWYCUOE. Chaotic output results from modifing both alphabets for each input letter.
See also in The book of science:
Readings in wikipedia:
Other readings: